For the past few days, some MySejahtera users have received SMS that contained a one-time password (OTP) for the app even though they didn’t request the code. In addition to that, others have also received spam e-mails that present themselves as if they came directly from the app’s helpdesk team.
One such user is journalist Haresh Deol who is the co-founder of the local news site, Twentytwo13. He noted in a tweet that the SMS made its way to his phone yesterday morning and has compiled a list of other users who have reported their experience on Twitter:
Others too received the same message
cc: @DrAdhamBaba @my_sejahtera pic.twitter.com/Df49wqMrU4— Haresh Deol 🇲🇾 (@HareshDeol) October 19, 2021
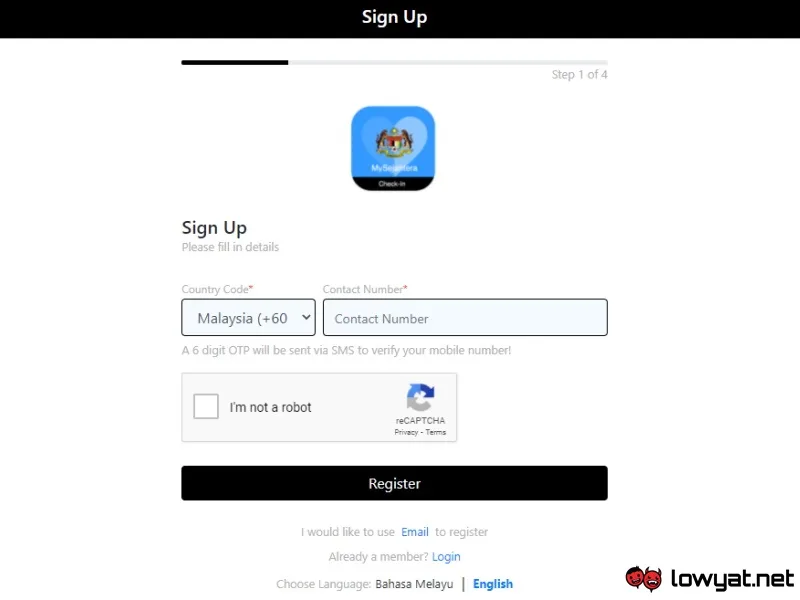
MySejahtera has since acknowledged the issue via a statement to local media outlets and said that it was caused by scripts that targeted the app’s registration system which relies on OTP code to verify the user’s identity. In addition to that, the team behind the app also pointed out that these scripts did not access users’ data and related API endpoints have since been blocked with a fix being scheduled to roll out tonight.
As it turns out though, full stack engineer Phakorn Kiong has detailed an API vulnerability relating to MySejahtera’s OTP system on 17 October through a post on Medium. The test command to call the API endpoint that Phakorn noted in his explanations then made its way to Lowyat.NET Forums on 18 October.
However, Phakorn has since updated the post to note that this particular exploit has been patched as of today.
Moving on to the spam e-mails, Malay Mail news editor Zurairi A.R had shared two samples that were sent to the newspaper’s editorial team and his inbox. Similar e-mails have also been sent through his work e-mail address which was never used to register for MySejahtera according to Zurairi.
Just heard about how @my_sejahtera's database is compromised, & right on time I got a troll email from its helpdesk. pic.twitter.com/hvOjttwAI5
— Zurairi A.R. (@zurairi) October 20, 2021
This particular issue has yet to be addressed by MySejahtera but it seems that it may have been caused by a weakness behind the app’s API as well. Before his take on MySejahtera’s OTP SMS system, Phakorn published a separate article on 16 October that discussed a programming oversight that blocked users from uploading a PDF version of their vaccination card to MySejahtera’s helpdesk.
During the troubleshooting process, Phakorn discovered some vulnerabilities within the API endpoint that made it possible for someone to send a mass e-mail with MySejahtera’s identity. He noted that MySejahtera has since implemented reCAPTCHA on the vaccination card upload page as of 18 October but it is not clear whether the team has managed to completely fix all the vulnerabilities listed by Phakorn.
There are also some concerns regarding the e-mail addresses that were targeted by the spammer. It is unclear whether they came from MySejahtera’s database or other sources, given how the spam e-mails were sent to Malay Mail’s editorial team and Zurairi’s work e-mail address as per what we mentioned earlier.
Nevertheless, MySejahtera’s team certainly have some explanations to do since millions of Malaysians use it on a daily basis and what we have seen here may tarnish its credibility.




