iPay88, a leading regional payment gateway provider based in Malaysia has suffered a breach involving its email API. While we are not able to ascertain at this point in time the extent of the breach, we can confirm that the compromised email API is, in turn, being used to send out very authentic sounding emails to unsuspecting customers – urging them to key in their credit card information to a fake site, aptly parked at ipay88.org (iPay88’s legitimate site is hosted on ipay88.com and ipay88.com.my).
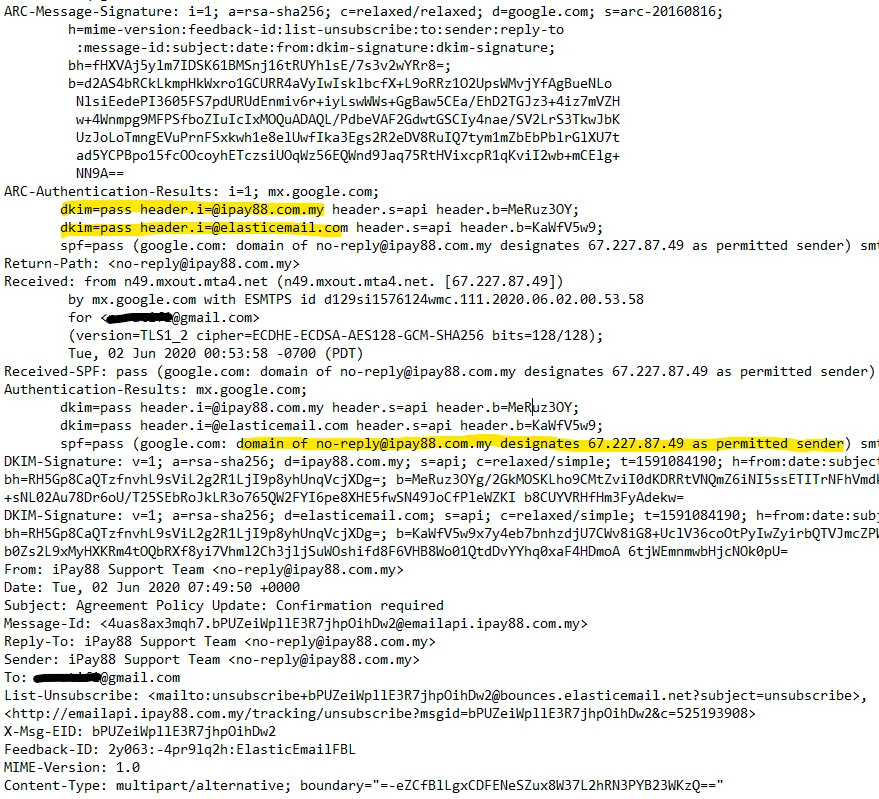
While most phishing emails are easily filtered out as spam by service providers like Google’s Gmail and Microsoft’s Outlook due to their dubious origins, this particular email carries all the necessary credentials to bypass all filters, simply because it is being sent from a bulk email service that has been pre-approved by iPay88.
A closer look at the email headers confirms that the phishing email originated from elasticemail.com, one of the two email services approved by iPay88 to send out emails to their customers and merchants. We have independently compared and verified legitimate emails and receipt mails sent out by iPay88 from both these email services even as far back as early 2019.
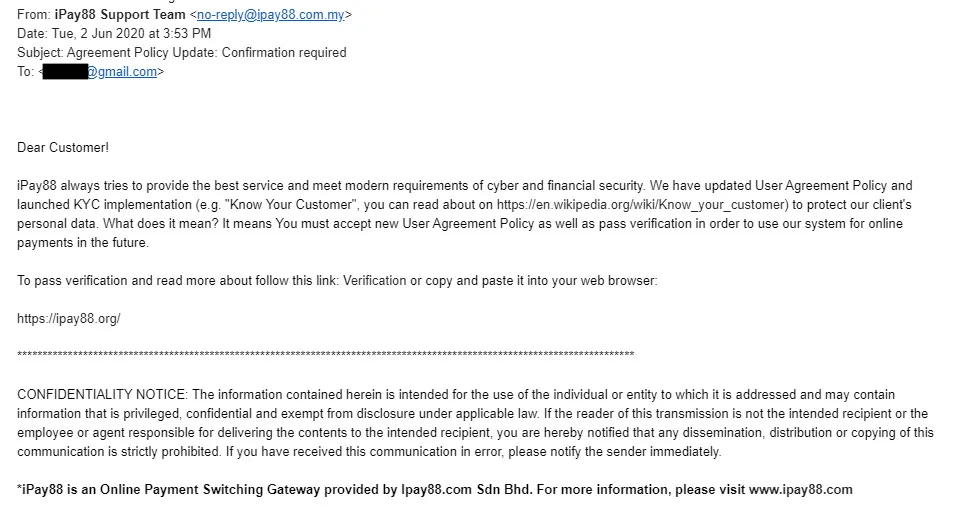
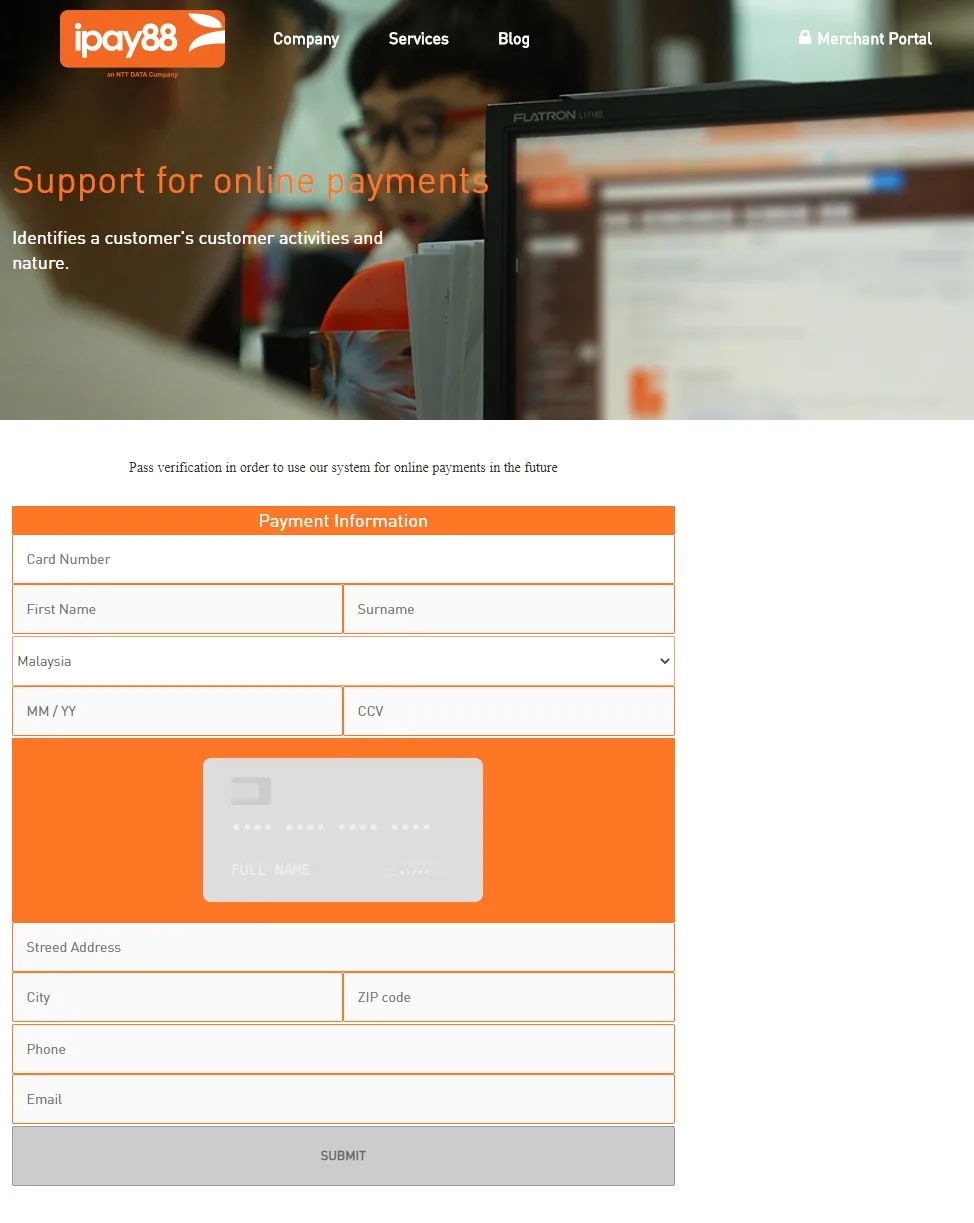
The email itself claims that there is an updated User Agreement Policy implemented by iPay88 that is required to ‘protect our client’s personal data’. As such, recipients of the email are encouraged to complete the verification by visiting ipay88.org, a fake phishing site set up to collect details as well as credit card information from unsuspecting users.
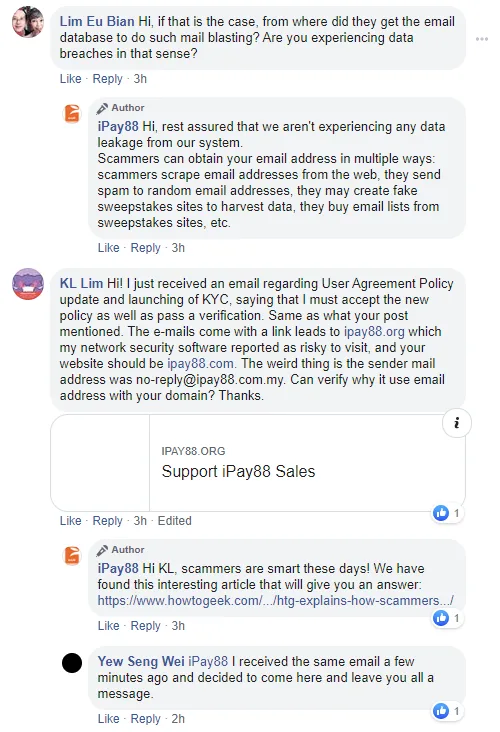
iPay88 however, via a posting on their Facebook page, has denied that they have suffered any breach, and are instead blaming it on scammers who are randomly sending out emails based on scraped addresses from email lists. We have reached out to iPay88 for more information on their claims.
If you’ve inadvertently keyed in your details at the ipay88.org phishing site, we urge you to immediately contact your bank to inform them that your card has been compromised and request for a replacement card.