Just to add on to your Monday morning blues, WPA2 (Wi-Fi Protected Access 2), which is the de-facto encryption method used by the majority of Wi-Fi routers around the world, is rumored to have been cracked.
While the actual exploit, called KRACK – short for Key Reinstallation AttaCK, has yet to be released, developers who have reviewed the flaw have confirmed that it is serious and could have widespread implications around the globe.
WiFi traffic between your computer, mobile phone and even right down to your CCTV cameras are encrypted to ensure that nobody else is able to intercept the data while it is transmitted. This is especially critical when sensitive data (for example, passwords) are passed from your device to the sites where it is intended to go.

Fortunately, most sites that handle sensitive data these days run on HTTPS, which means that on top of the WiFi encryption, the data is also encrypted again via a certificate unique to each site.
https://twitter.com/kennwhite/status/919522184384729089
However, there are still millions of sites and services online which are still running on the non-secure HTTP protocol, and a broken WPA2 encryption protocol could essentially allow someone with enough knowledge of the flaw to intercept and decipher all traffic flowing through that particular WiFi network.
US-CERT has become aware of several key management vulnerabilities in the 4-way handshake of the Wi-Fi Protected Access II (WPA2) security protocol. The impact of exploiting these vulnerabilities includes decryption, packet replay, TCP connection hijacking, HTTP content injection, and others. Note that as protocol-level issues, most or all correct implementations of the standard will be affected. The CERT/CC and the reporting researcher KU Leuven, will be publicly disclosing these vulnerabilities on 16 October 2017.
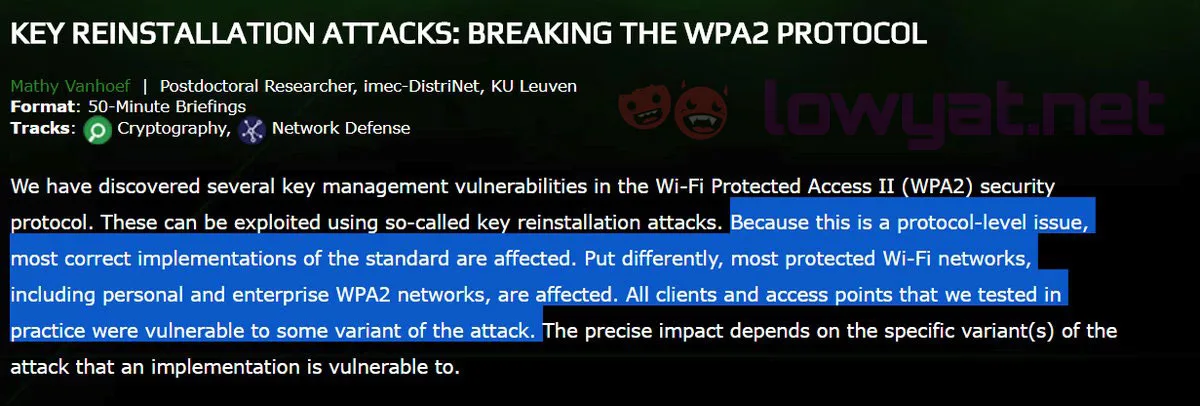
According to Mathy Vanhoef, who disclosed the vulnerabilities earlier today, the attack works against almost all unpatched WiFi networks currently being deployed around the world, and Android devices are notably vulnerable to an “exceptionally devastating” variant of the Wi-Fi attack.
The exploit itself is patchable by router manufacturers, but at this point in time, only Mikrotik seems to have rolled out a patch for vulnerabilities which first came to light in early August.
The researches also caution against switching to WPA or WEP as these protocols have even less security compared to WPA2. They recommend continuing to use WPA2 until patches are delivered.
For more information, this FAQ on the vulnerability by Aruba Networks is a recommended read – especially if you’re a System or Networks Administrator in charge of networks that require immediate attention.



