A study has found that AMD processors made from 2013 onwards are vulnerable to a series of side-channel attacks. The research, which was carried out by researchers at the Graz University of Technology in Austria, classified the attacks as “Collide + Probe” and “Load + Reload”.
Both side-channel attacks are designed to attack the L1D cache way predictor. Where data is stored on AMD processors. As per Techspot’s explanation, the exploits – dubbed the “Take A Way” flaws – are first attacked with the attacker picking a corresponding address with the target data. From there, the attacker can then create a link based on the address, thus enabling access to the address to be quicker with the next infiltration.
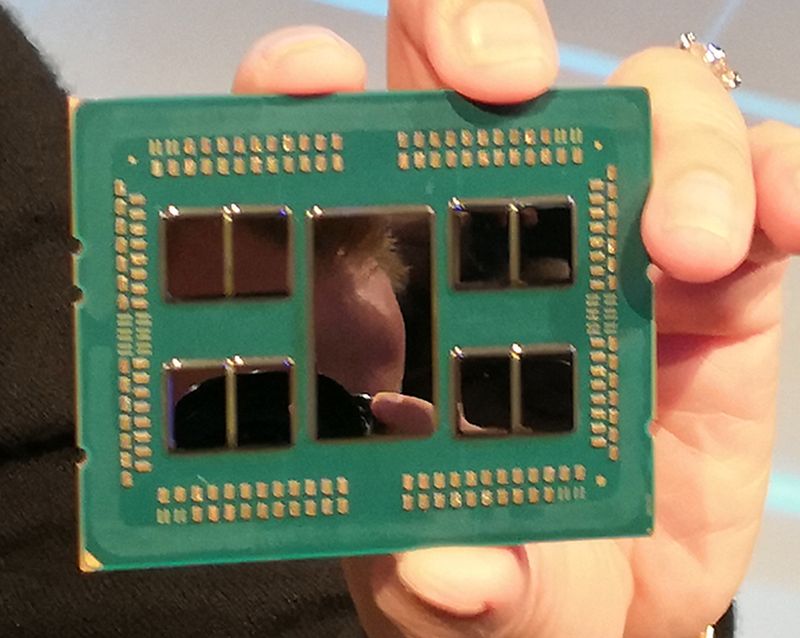
At the time of writing, the flaw effectively affects a whole list of AMD processors. Including older Athlon, FX, and the current mainstream Ryzen and HEDT Threadripper CPUs.
Also, the research team has already informed AMD about its findings back in August, giving the CPU maker more than enough time to patch up the security vulnerabilities in its processors. If you’re interested, you can read the team’s research paper in the source link, but be warned that it is a bit dry.
This isn’t the first time AMD’s processors have come under threat of security vulnerabilities. Back in 2018, an Israeli-based group known as CTS Labs surprised both AMD and the tech industry when it informed AMD of its findings. 24 hours before it went public.
(Source: Techspot, Graz University of Technology)