Following up on our report on 19th October, we can now confirm that roughly 46.2 million mobile phone numbers from Malaysian telcos and mobile virtual network operators (MVNO) have been leaked online.
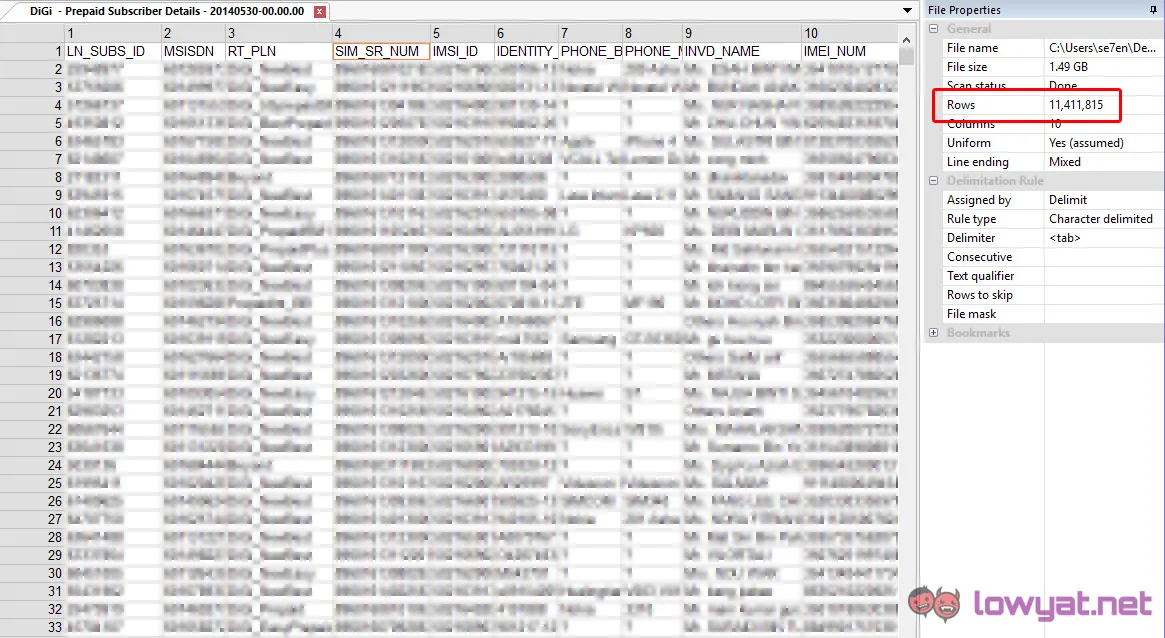
The leak includes postpaid and prepaid numbers, customer details, addresses as well as sim card information – including unique IMEI and IMSI numbers.
Time stamps on the files we downloaded indicate the leaked data was last updated between May and July 2014 between the various telcos. The exact numbers, broken down by telco/MVNO provider, and further broken down by prepaid or postpaid segments are as below.
Telco/MVNO | Total Records | Last Updated |
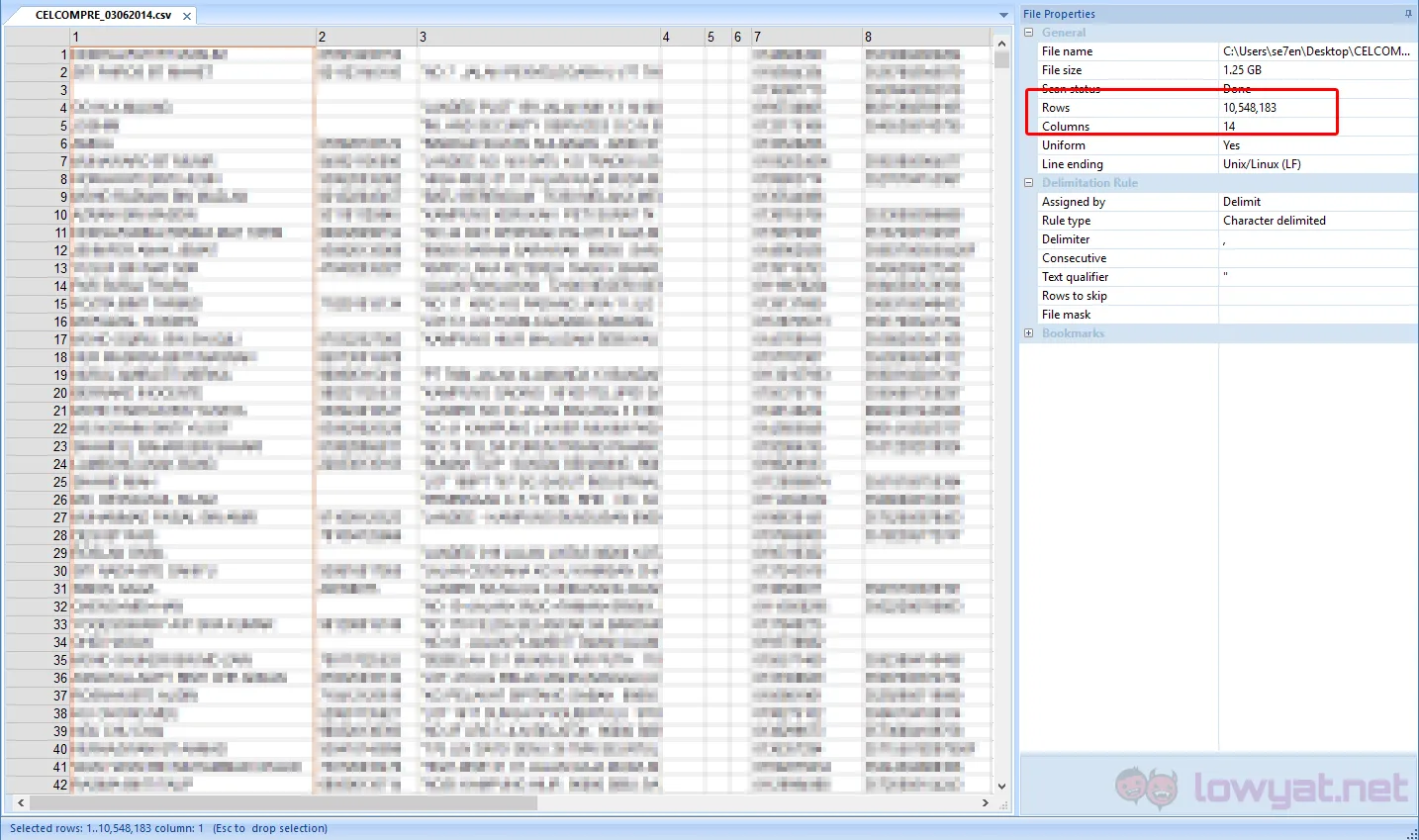
Celcom Prepaid | 10,548,183 | 03-06-2014 |
Celcom Postpaid | 4,194,315 | 03-06-2014 |
Digi Prepaid | 11,411,815 | 30-05-2014 |
Digi Postpaid | 2,036,730 | 30-05-2014 |
Umobile postpaid + prepaid | 3,866,672 | 30-05-2014 |
Maxis Postpaid | 2,840,741 | 29-07-2014 |
Maxis Hotlink | 9,562,019 | 29-07-2014 |
Friendi Mobile | 43,523 | 29-06-2014 |
MerchantradeAsia | 446,203 | 07-07-2014 |
Tunetalk | 597,276 | unknown |
Redtone | 246,613 | 30-05-2014 |
XOX | 79,139 | 30-05-2014 |
Altel | 24,279 | unknown |
PLDT | 68,900 | 17-07-2014 |
EnablingAsia | 212,139 | 30-04-2014 |
Total | 46,178,547 |
We are also now fairly certain that the individual who tried to sell the data two weeks back acquired the data in a similar fashion that we did, and tried to make a quick profit by attempting to sell it on our Forums.
We have shared all details regarding the data that we uncovered, as well as how we managed to obtain all the data with the MCMC last week.
The MCMC is following up with the relevant agencies to determine the source of the breach, but we now believe that the data was already being traded online much earlier then we first estimated. Based on the condition of the files that we obtained, we are quite certain that it has already changed hands more than once.
Medical Practitioners Database
Aside from the telco database, we can now also confirm that a total of 3 databases belonging to the Malaysian Medical Council (MMC), the Malaysian Medical Association (MMA), as well as the Malaysian Dental Association (MDA) have also been leaked.
Database | Total Records | Last Updated |
Malaysian Medical Association (MMA) | 15,965 | 05-02-2015 |
Malaysian Medical Council (MMC) | 61,062 | 06-03-2015 |
Malaysian Dental Association (MDA) | 4,282 | 25-01-2015 |
Total | 81,309 |
As mentioned in our previous post, these medical databases include personal information, MyKad numbers, mobile/work/home phone numbers, as well as work and residential addresses.
Remedial Action
We first highlighted about this data breach on 19th October, and we are extremely concerned that no remedial action has been taken by the service providers involved to protect those that have been affected by the breach.
In this day where everything is stored electronically, data security breaches are not something to be taken lightly. Any entity, public or private, that stores proprietary or sensitive data electronically could end up having that data stolen or lost – with catastrophic consequences.
While it is the task of the authorities to narrow down the source of the breach, and ensure that a similar incident doesn’t happen again, the key to containing any more serious damage is protecting the individuals affected by the breach.
We are urging the telco and MVNO companies mentioned above to alert and start immediately replacing the SIM cards of all affected customers, especially those who have not updated their SIM cards since 2014. While the leaked data alone isn’t sufficient to clone the SIM cards, the information available can be exploited to initiate multiple social engineering attacks against affected users.
Public awareness of the data breach, as well as vigilance are critical to keeping consumers safe after a data breach. The United States have enacted the Security Breach Notification Laws across 48 states that requires private or governmental entities to notify individuals of security breaches of information involving personally identifiable information – with California enacting it as early as 2002.
[hide]
Disclaimer: All data we recovered is currently encrypted and stored in a single location. We will be destroying all data that we have retrieved by Friday, 3 November at 12pm. Data owners, please contact us should you require us to handover the data.[/hide]



