Malware targeting mobile platforms is becoming increasingly common as more people adopt smartphones. This has had the unfortunate effect of causing criminals to build malware that is becoming more advanced and difficult to detect. Thus far, it has culminated in Triada – an Android based Trojan that is comparable to PC based malware in terms of complexity.
Triada itself isn’t exactly a single Trojan, but rather a family of 11 different Trojan families that all use root privileges to install unwanted apps in the phone. Three of these families – Ztorg, Gorpo and Leech – even work together to accomplish the goal of creating an advertising botnet that allows criminals access to infected smartphones and tablets.
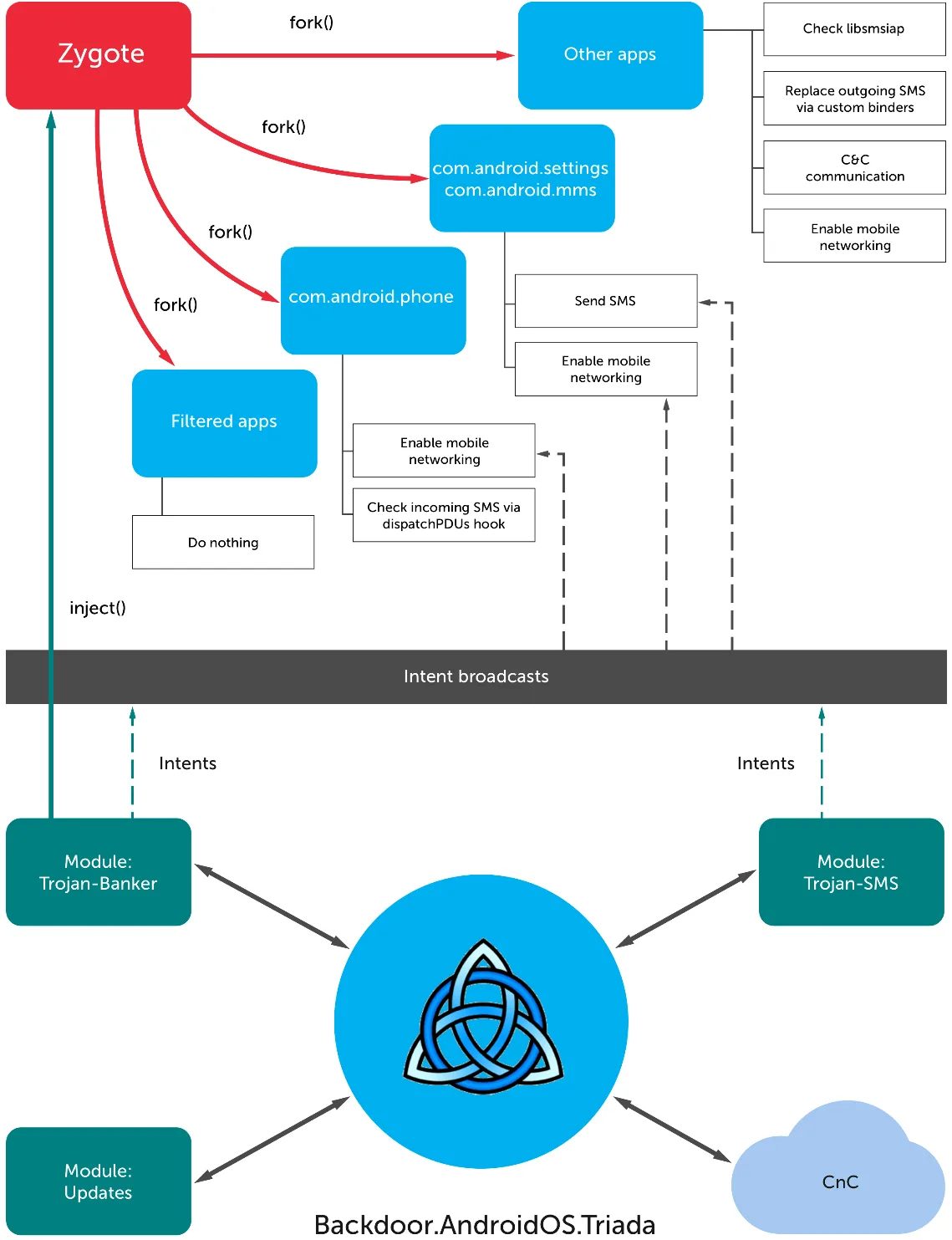
These Trojans gain access to Zygote, which is the parent application process on all Android devices. All apps go through Zygote to launch, and Triada hijacks this process and becomes part of the app process. Essentially, it will hide malware in perfectly legitimate apps if given the chance. This is particularly interesting because it is the first time that this exploit has been seen in the wild, although a proof of concept has been demonstrated before.
Once the Triada has gained access to the device, it will proceed to hide itself using techniques not yet seen on mobile malware. The Trojan will use stealth techniques like embedding itself in every working process and existing only in the phone RAM. This makes it extremely difficult to detect knowing what to look for.
Kaspersky reports that the malware has been active in Russia, Ukraine, India, and across the APAC region. Criminals in these regions have been using the access to hijack SMS messages meant to purchase content through Google Play. What happens is that the malware will alter the destination of the SMS, which in turn redirects the payment to their own system. In other words, the criminals will end up stealing payment meant for developers, making it more difficult to notice that something is wrong with the device.



