
The fallout from the massive 400 GB leak from the Hacking Team continues as researchers have discovered an unpatched vulnerability in Flash. It turns out that the Italian spyware maker had discovered this vulnerability, and used it as an attack vector for its products. A couple of other vulnerabilities in Windows and SELinux also turned up in the documentation as well.
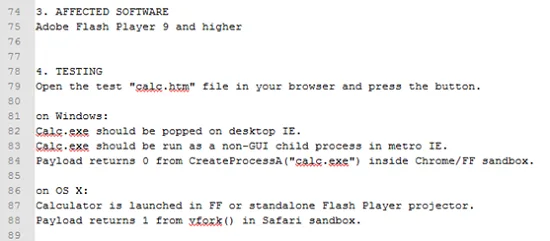
Hacking Team had apparently called the exploit “the most beautiful Flash bug for the last four years”. The exploit has been confirmed to work against current versions of Flash, especially against people viewing the content on Internet Explorer. It is unknown if the exploit works on other browsers, although Symantec is assuming that it does. Perhaps erring on the side of caution.
Adobe has said that it is aware of the vulnerability and will be pushing out a patch to close it this week. The company says that there is no indication that the exploit is being used at this point in time, although it almost certainly is if Hacking Team has been using it to deploy spyware.
The vulnerability in the Windows kernel appears to have existed since Windows XP, and can be used to escalate user privileges to increase the attacker’s access to the target machine. On the ther hand, the SELinux exploit indicates the possibility that it could be used against Android devices that incorporate this particular Linux module.
It isn’t surprising that the Hacking Team information contains details of previously unknown exploits and vulnerabilities. The spyware needs a way to infect target machines, and this is the most obvious manner of deploying the tools. While this information is less impressive than the list of Hacking Team customers, it may prove to be the more dangerous for the average person.
[Source: Ars Technica]



