A new low tech malware campaign has been making the round, and has successfully raked in over US$1 million (about RM3.7 million) from unsuspecting victims. IBM security identified the campaign from the variant of the Dyre malware, leading to the name Dyre Wolf.
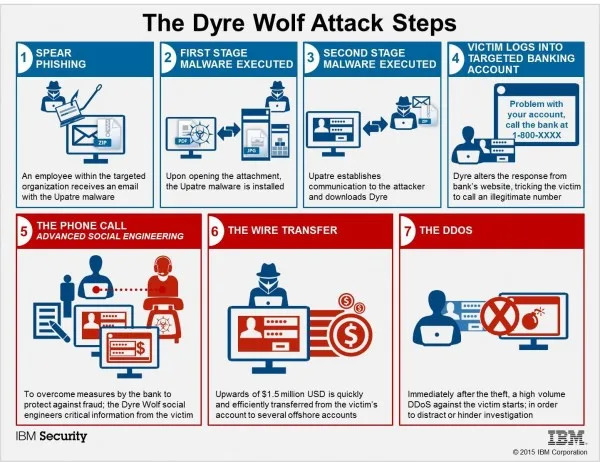
Cybercriminals have been using Dyre since 2014 to target organisations, but this particular version takes on an additional twist. Dyre Wolf uses spear phishing techniques to target organisations that often deal with large amounts of money wire transfers. It then lays in wait until the user attempts to log into one of the hundreds of bank websites it has been set up to monitor. When this happens, a screen will load telling the user that the site is down for maintenance and they should call the provided number for help.
Once the number is called, it is a small matter of social engineering the user into giving up their banking details. IBM notes that these particular cybercriminals are extremely bold in using the same phone number for each website; and somehow know precisely when the victims will call and which bank they are looking for.
Interestingly enough, Dyre is a known piece of malware; and yet this version managed to slip undetected past the victims’ security systems. It could be that the victims failed to keep their anti-virus software up to date, although the report did not mention the level of security implemented by the victims.
The low tech style of this attack even manages to bypass two stage authentication, reminding everyone that the weakest link in any security happens to be between the chair and the keyboard. IBM itself says that 95-percent of all successful cyber-attacks involved some sort of human error.
Dyre Wolf is still operating in the wild, and still a threat to organisations. However, considering that it uses the same phone number for every attack, it could only be a matter of time before the identity of the cybercriminals are discovered.
[Source: IBM via Ars Technica]