Intel has recently revealed that quite a number of its processors are affected by security vulnerabilities. Originally discovered by external security researchers including Mark Ermolov and Maxim Goryachy of Positive Technologies Research, the issue is rather serious since these vulnerabilities could ultimately allow attackers to take over user’s system remotely.
Specifically, the issue might lead to unauthorized access to Intel Management Engine, Intel Server Platform Service, or Intel Trusted Execution Engines. All of these features are essential to the operation for most of Intel’s processors out there which is why the list of affected processors are quite extensive:
- 6th, 7th, and 8th generation Intel Core Processor Family
- Intel Xeon Processor E3-1200 v5 and v6 Product Family
- Intel Xeon Processor Scalable Family
- Intel Xeon Processor W Family
- Intel Atom C3000 Processor Family
- Apollo Lake Intel Atom Processor E3900 series
- Apollo Lake Intel Pentium Processors
- Intel Celeron N and J series Processors
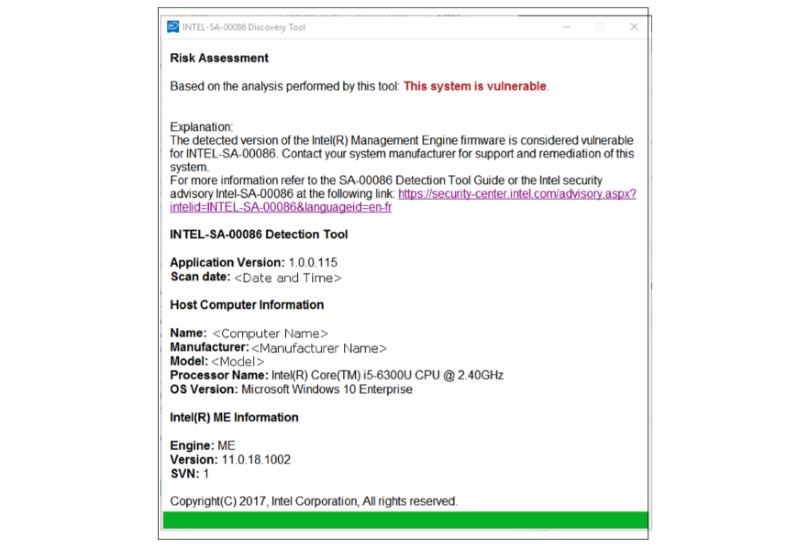
With that, the security vulnerabilities have pretty much put millions of PCs out there at risk. If you are wondering whether your machine is affected by this vulnerability, Intel has actually released a downloadable tool that can help you verify the status of your PC:
 If you are using Intel-based Mac PCs, you don’t have to worry about these vulnerabilities as they don’t affect your machines.
If you are using Intel-based Mac PCs, you don’t have to worry about these vulnerabilities as they don’t affect your machines.
Meanwhile, various manufacturers are already working together with Intel to come out with fixes for their products. However, it might take some time for them to cover everyone given the long list of products that are affected by this issue.