If you’re an iPhone user still on older versions of iOS, now is probably a good idea to update your device. Following the discovery of the Coruna hacking kit, researchers at Google and cybersecurity firms iVerify and Lookout have found a new exploit. Called “DarkSword”, the new exploit specifically targets multiple versions of iOS 18, namely iOS 18.4 through iOS 18.7.
Much like Coruna, DarkSword has been deployed in “watering hole” attacks, which involve embedding malware in specific websites. But while the former largely targeted Ukrainian users, the new exploit has been used in campaigns against users in other regions, Malaysia included.
What is DarkSword?
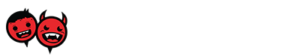
As per the reports, DarkSword is a “fileless” hack, which means that it does not install spyware that lingers long after the data has been stolen. Instead, it uses a much stealthier hit-and-run approach that leaves fewer traces. By leveraging vulnerabilities in the operating system, DarkSword can take control of legitimate processes on the device. This happens with little to no action from the user, by the way.
The hack begins as soon as the device visits an infected website. Once the iPhone encounters a malicious iframe embedded in the webpage, DarkSword exploits six vulnerabilities to give itself kernel privileges. Then, it deploys payloads to steal sensitive information. Among the things DarkSword can access include passwords, messages, iCloud content, and cryptocurrency wallets.

After successfully collecting and exfiltrating the data, it deletes itself. According to the reports, DarkSword’s dwell time on a device is “in the range of minutes”, although this does hinge on how much data it steals. Also worth noting is that compared to Coruna, DarkSword is less complex, although both hacks employ sophisticated methods.
More widespread hacking campaigns
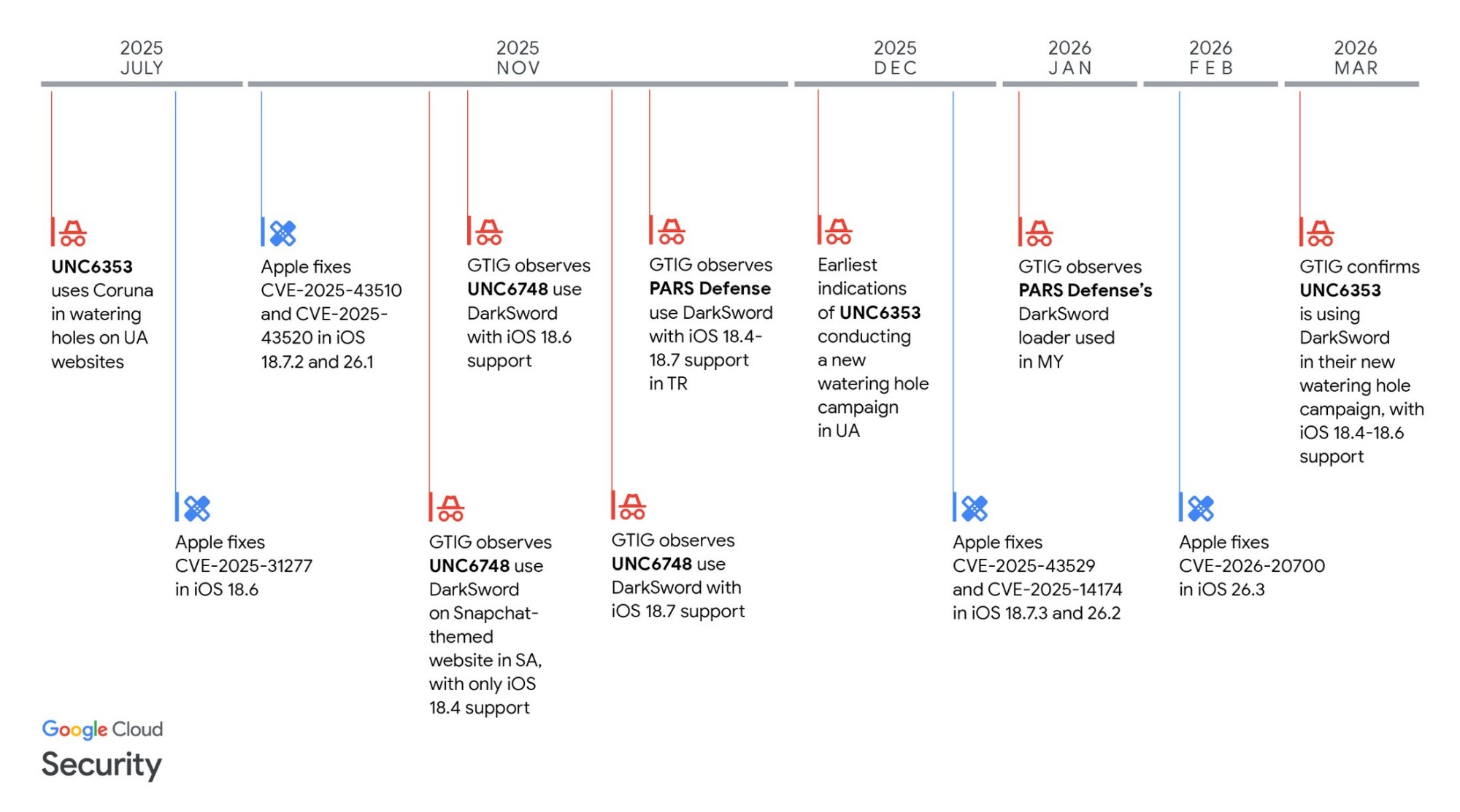
According to the reports, DarkSword was spotted as early as late 2025, around the same time Coruna was discovered. In fact, the two were found on the same servers, and DarkSword was discovered while the firms were investigating Coruna. Given this information, one may assume that both of these tools share a creator. However, it is unclear whether this is the case. Coruna has been linked to a company called Trenchant, which creates hacking and surveillance tools for the US government and its allies.
On the other hand, DarkSword’s origins remain uncertain. Regardless, the attackers wielding it may not necessarily be its developers. The fact that two distinct powerful iOS exploits have been found suggests that there may be a “secondhand market” for these tools. This allows groups with fewer resources to deploy malware against users.
In fact, this may already be happening with DarkSword. According to iVerify cofounder and researcher Matthias Frielingsdorf, the hackers have left the full, unobscured DarkSword code online. This includes explanatory comments in English that detail each component, essentially providing anyone with a manual to weaponise the tool.
Google has so far observed DarkSword in Ukraine, Saudi Arabia, Turkey, and Russia. And of course, as mentioned earlier, it has also been seen on our shores. As outlined in Google’s report, the campaigns in Malaysia and Turkey were linked to Turkish commercial surveillance vendor PARS Defense.

It is currently uncertain whether DarkSword has been deployed elsewhere. However, given its stealthy nature, it may be difficult to identify which websites have been infected. It’s possible that attackers may use it for financially-focused cyber crimes, as the exploit can be used to gain access to cryptocurrency wallet information.
Update to stay safe
As scary as it may sound, DarkSword is specialised for specific versions of iOS. The good news is that it targets software that is out of date, and Apple has already released updates to fix these vulnerabilities. So, it goes without saying that those who can update their devices should do so as soon as possible. iVerify recommends updating to iOS 18.7.6 or iOS 26.3.1, as this will “mitigate all vulnerabilities” involved in the attack chains.
Of course, this is well and good for iPhones that can run these new software versions. Older models that cannot upgrade still remain vulnerable to attacks. Granted, Apple could release patches for such devices, as it has recently done. But in the meantime, users can activate Lockdown Mode. Other than that, iVerify notes that the exploits are ineffective on the iPhone 17 with Memory Integrity Enforcement (MIE) enabled.
 In addition to this, the identified malicious domains have been blocked blocked by Apple Safe Browsing in the Safari web browser. This ensures that no further exploitation can occur.
In addition to this, the identified malicious domains have been blocked blocked by Apple Safe Browsing in the Safari web browser. This ensures that no further exploitation can occur.
For now, it is unclear how many devices are at risk. According to Apple’s latest iOS usage stats for developers, around 24% of devices are still running iOS 18. That said, there isn’t much detail here, so exact numbers remain uncertain, though estimates range from 220 million to 270 million iPhones. In any case, it’s typically a good idea to ensure your electronics are up to date.
(Source: Google, iVerify, Lookout, WIRED)

[UPDATE: 9:16am, 20 March 2026]
In light of this discovery, the Malaysian Communications and Multimedia Commission (MCMC) has issued a statement urging Apple users to immediately update their iOS devices to the latest software versions. In a statement, the commission reiterated the fact that Apple has already rolled out patches to address the vulnerabilities.
MCMC also warned that out-of-date devices may be exposed to security risks, including unauthorised access to data, installation of malware or spyware, theft of messages, and possible monitoring. Additionally, the commission advised users to enable automatic updates and practice safe digital habits. Some examples include avoiding suspicious sites, only installing applications from the Apple App Store, restarting devices after updates, and staying alert to unusual behaviour.
(Source: Bernama)