Activity from the infamous Lazarus hackers has been detected in Malaysia. While the malware was discovered before it could be used to do any damage, it shows a group that has a much further reach than previously imagined.
The Lazarus group has been involved in several high profile cyberattacks over the last couple of years. It is the prime suspect in the attack on Sony Pictures that completely crippled the film studio for months, and has also been implicated in the 2016 theft of $81 million from the Central Bank of Bangladesh.
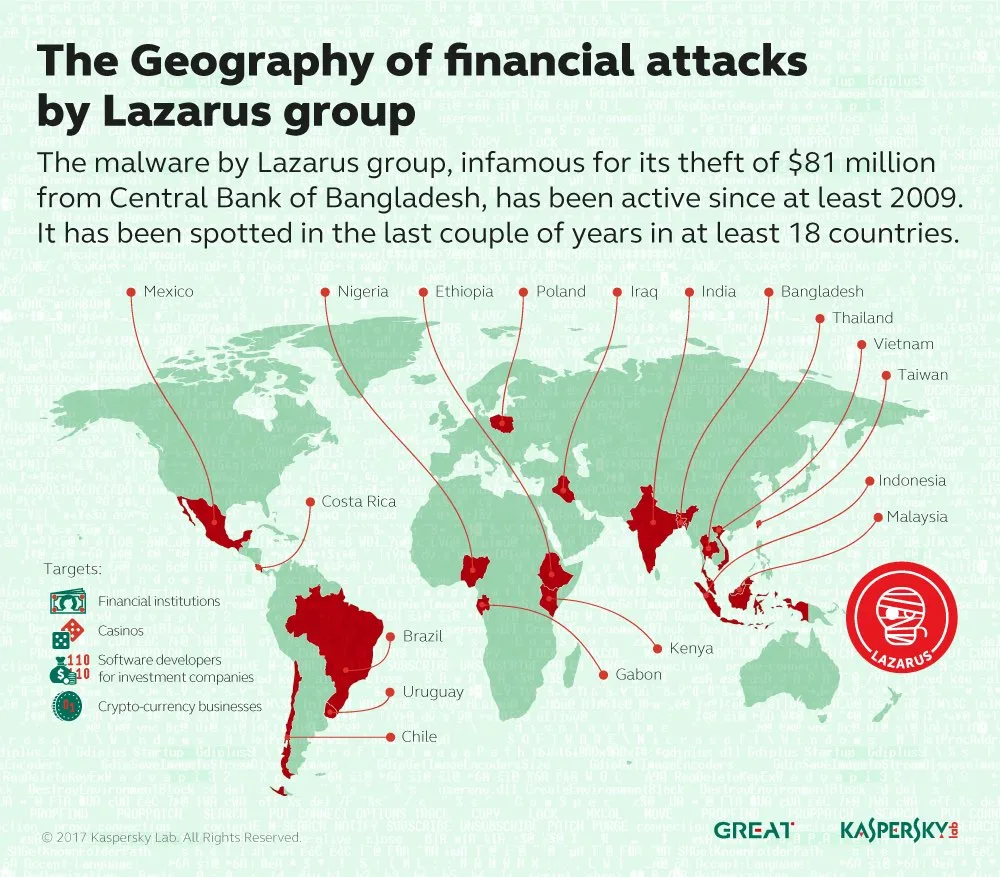
Kaspersky Lab, who recently completed a year-long investigation into the group, discovered samples of the group’s activity in 18 countries around the world. The malware used by Lazarus appears to have dated back to 2009; and has largely targeted financial instutions, casino software development, and crypto-currency businesses.
Samples of the Lazarus malware in Malaysia were detected relatively late, only being recorded in December 2016. Kaspersky has not specifically said which industries were affected by the malware, but we are guessing that it would be banks and financial institutions. Considering that there is a lack of the other two favoured targets in this country.
The identity of the Lazarus group is still unknown, although many signs point towards state sponsored actors from North Korea. The US government has officially accused the military dictatorship of being behind the attack on Sony Pictures; although no evidence has been released to the public. Still, Kaspersky’s own investigation points to the malware connecting to servers located in North Korea as well.
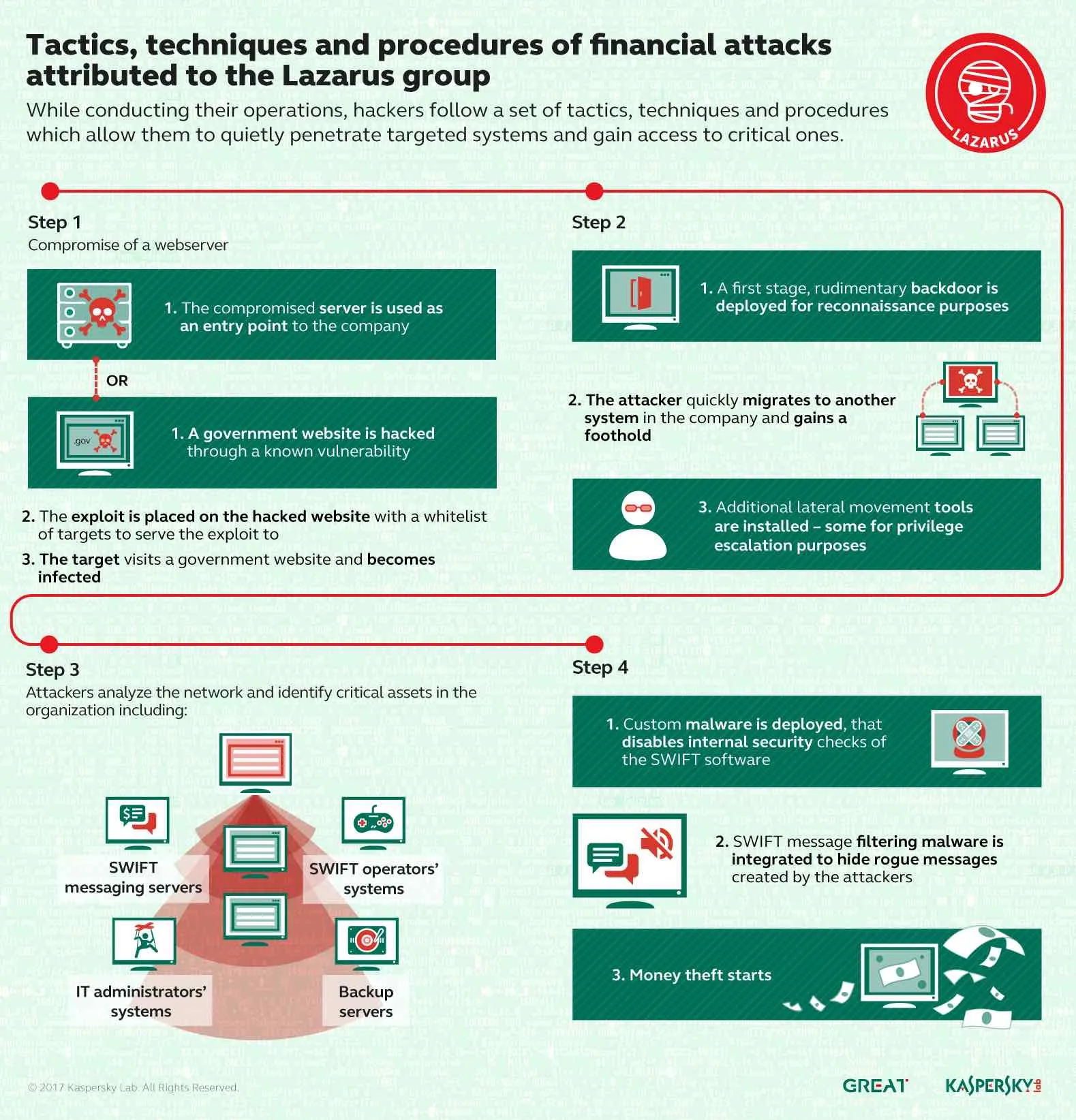
There’s no real threat of Lazarus in Malaysia yet, seeing that the malware has been detected and contained. Then again, Lazarus has been known to be extremely patient in its approach. The group will infiltrate the target servers and watch its activity for months at a time before making a move. As was the case with both Sony Pictures and the Central Bank of Bangladesh.